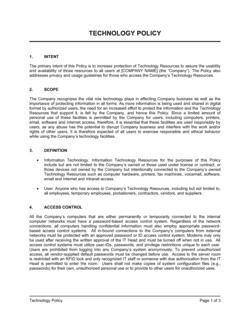
- Acceptable use policy (AUP)
- A rule document telling employees what they may and may not do with company IT systems, devices, and data.
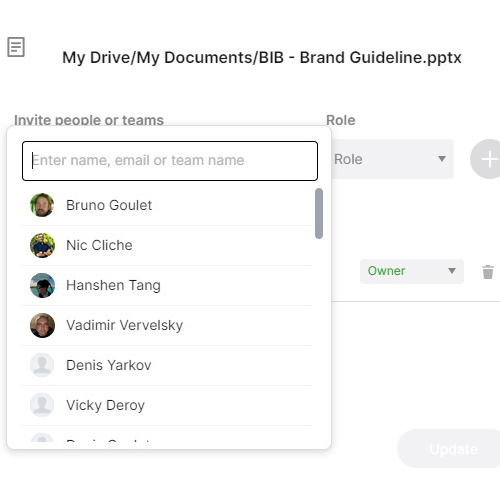
- Access control
- The process of granting or restricting user permissions to systems, applications, and data based on defined authorization rules.
- Data classification
- A scheme that groups data into sensitivity tiers (e.g., public, internal, confidential, restricted) to determine how each tier must be handled and protected.
- Endpoint security
- Controls applied to individual devices — laptops, phones, servers — to prevent them from being used as entry points for attacks.
- Incident response
- The structured process an organization follows to detect, contain, investigate, and recover from a security breach or cyberattack.
- Information security
- The broader discipline of protecting data in all forms — digital and physical — from unauthorized access, disclosure, or destruction.
- Multi-factor authentication (MFA)
- A login method that requires two or more independent verification steps, such as a password plus a one-time code, to reduce unauthorized access.
- Network segmentation
- Dividing a computer network into separate zones so that a breach in one zone cannot automatically spread to others.
- Patch management
- The process of regularly applying software updates to fix known security vulnerabilities in operating systems and applications.
- Security posture
- An organization's overall readiness to detect, prevent, and respond to cyber threats, based on its policies, controls, and practices.
- Threat landscape
- The range of cyber threats an organization faces, including phishing, ransomware, insider threats, and supply-chain attacks.
- Zero trust
- A security model that requires every user and device to be verified before accessing any resource, regardless of whether they are inside or outside the corporate network.