Network Security Policy Template
Sample of Document Content
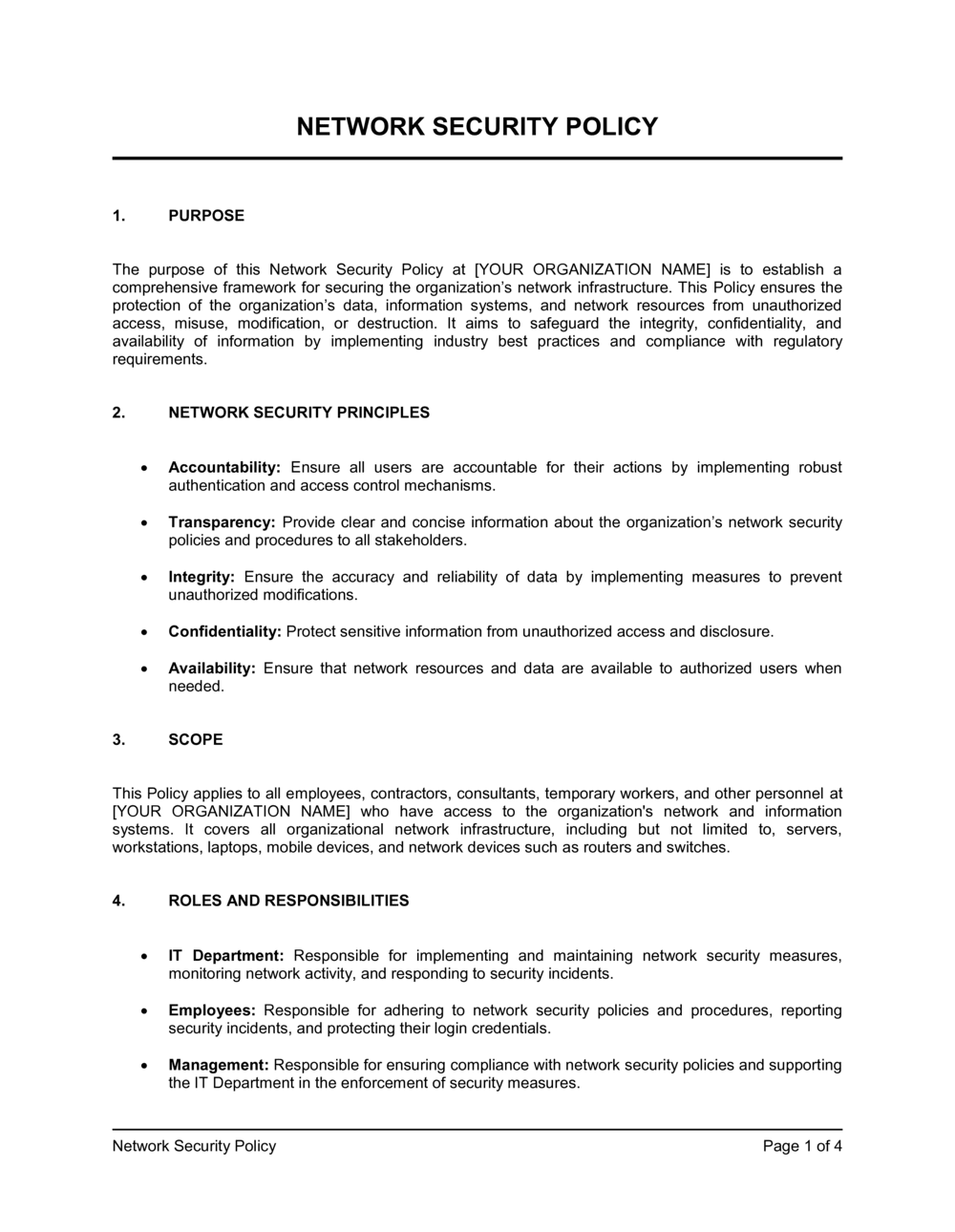
This network security policy template has 4 pages and is a MS Word file type listed under our legal agreements documents.
Network security policy template
NETWORK SECURITY POLICY PURPOSE The purpose of this Network Security Policy at [YOUR ORGANIZATION NAME] is to establish a comprehensive framework for securing the organization's network infrastructure. This Policy ensures the protection of the organization's data, information systems, and network resources from unauthorized access, misuse, modification, or destruction. It aims to safeguard the integrity, confidentiality, and availability of information by implementing industry best practices and compliance with regulatory requirements. NETWORK SECURITY PRINCIPLES Accountability: Ensure all users are accountable for their actions by implementing robust authentication and access control mechanisms. Transparency: Provide clear and concise information about the organization's network security policies and procedures to all stakeholders. Integrity: Ensure the accuracy and reliability of data by implementing measures to prevent unauthorized modifications. Confidentiality: Protect sensitive information from unauthorized access and disclosure. Availability: Ensure that network resources and data are available to authorized users when needed. SCOPE This Policy applies to all employees, contractors, consultants, temporary workers, and other personnel at [YOUR ORGANIZATION NAME] who have access to the organization's network and information systems. It covers all organizational network infrastructure, including but not limited to, servers, workstations, laptops, mobile devices, and network devices such as routers and switches. ROLES AND RESPONSIBILITIES IT Department: Responsible for implementing and maintaining network security measures, monitoring network activity, and responding to security incidents. Employees: Responsible for adhering to network security policies and procedures, reporting security incidents, and protecting their login credentials. Management: Responsible for ensuring compliance with network security policies and supporting the IT Department in the enforcement of security measures. NETWORK ACCESS CONTROL User Authentication: All users must authenticate using unique usernames and passwords. Strong password policies must be enforced, requiring regular password changes and complexity requirements. Access Rights: Access to network resources must be granted, based on the principle of least privilege. Users should only have access to the resources necessary to perform their job functions. Network Segmentation: Networks must be segmented, based on functionality and security requirements to limit the spread of potential security breaches. SECURITY MEASURES Firewalls: Firewalls must be implemented to control incoming and outgoing network traffic, based on predetermined security rules.
Part of your Business Operating System
Reviewed on

Sample of Document Content
This network security policy template has 4 pages and is a MS Word file type listed under our legal agreements documents.
Sample of our network security policy template:
NETWORK SECURITY POLICY PURPOSE The purpose of this Network Security Policy at [YOUR ORGANIZATION NAME] is to establish a comprehensive framework for securing the organization's network infrastructure. This Policy ensures the protection of the organization's data, information systems, and network resources from unauthorized access, misuse, modification, or destruction. It aims to safeguard the integrity, confidentiality, and availability of information by implementing industry best practices and compliance with regulatory requirements. NETWORK SECURITY PRINCIPLES Accountability: Ensure all users are accountable for their actions by implementing robust authentication and access control mechanisms. Transparency: Provide clear and concise information about the organization's network security policies and procedures to all stakeholders. Integrity: Ensure the accuracy and reliability of data by implementing measures to prevent unauthorized modifications. Confidentiality: Protect sensitive information from unauthorized access and disclosure. Availability: Ensure that network resources and data are available to authorized users when needed. SCOPE This Policy applies to all employees, contractors, consultants, temporary workers, and other personnel at [YOUR ORGANIZATION NAME] who have access to the organization's network and information systems. It covers all organizational network infrastructure, including but not limited to, servers, workstations, laptops, mobile devices, and network devices such as routers and switches. ROLES AND RESPONSIBILITIES IT Department: Responsible for implementing and maintaining network security measures, monitoring network activity, and responding to security incidents. Employees: Responsible for adhering to network security policies and procedures, reporting security incidents, and protecting their login credentials. Management: Responsible for ensuring compliance with network security policies and supporting the IT Department in the enforcement of security measures. NETWORK ACCESS CONTROL User Authentication: All users must authenticate using unique usernames and passwords. Strong password policies must be enforced, requiring regular password changes and complexity requirements. Access Rights: Access to network resources must be granted, based on the principle of least privilege. Users should only have access to the resources necessary to perform their job functions. Network Segmentation: Networks must be segmented, based on functionality and security requirements to limit the spread of potential security breaches. SECURITY MEASURES Firewalls: Firewalls must be implemented to control incoming and outgoing network traffic, based on predetermined security rules.
Create Standard Documents That Define How Your Business Runs.
Agreements, policies, and plans — all structured inside one Business Operating System.
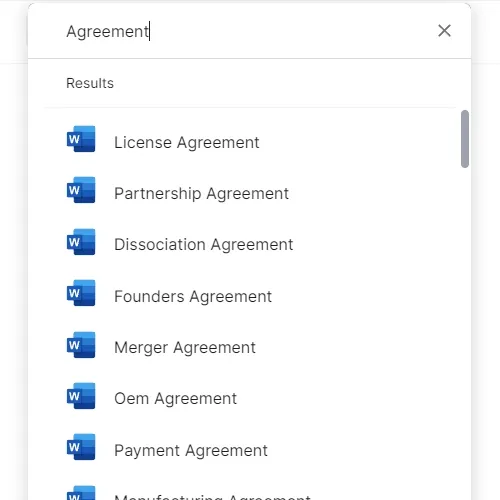
Download or open template
Access over 3,000+ business and legal templates for any business task, project or initiative.
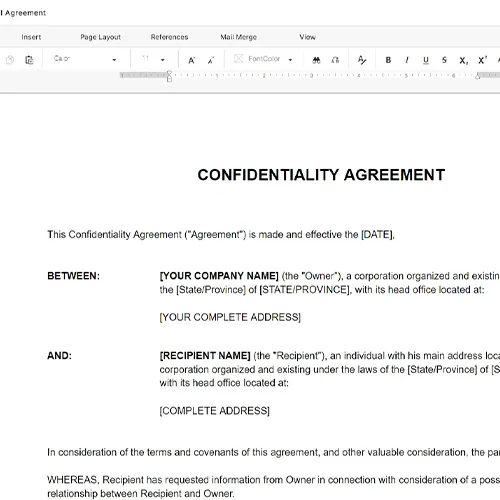
Edit and fill in the blanks
Customize your ready-made business document template and save it in the cloud.
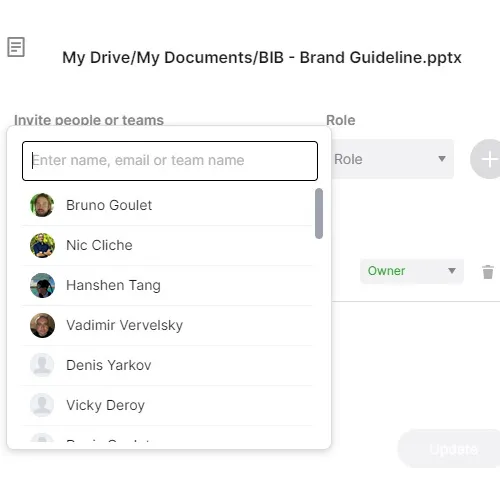
Save, Share, Export, or Sign
Share your files and folders with your team. Create a space of seamless collaboration.
Run Your Business With a System — Not Scattered Tools
Stop downloading documents. Start operating with clarity. Business in a Box gives you the Business Operating System used by over 250,000 companies worldwide to structure, run, and grow their business.


