Cyber Security Policy Template

Fortifying Digital Integrity with a Cybersecurity Policy
In today's digital age, where technology permeates every aspect of business operations, protecting information assets against cyber threats is paramount. A Cybersecurity Policy forms the backbone of an organization's security framework, establishing comprehensive guidelines that govern the use, management, and protection of electronic information.
This policy is a critical tool, outlining the standards for cybersecurity measures across the organization, including data protection protocols, access control mechanisms, and response strategies for security incidents. It not only ensures the safeguarding of confidential and sensitive information but also fosters a culture of security awareness and compliance among all employees. This document transcends traditional IT management; it is about embedding security into the very fabric of organizational operations to mitigate risks and maintain trust with stakeholders.
What is a Cybersecurity Policy Template?
A Cybersecurity Policy template serves as a structured guideline that details the essential components of establishing effective cyber defences. This includes the identification of critical information assets, risk management procedures, security practices for employees, and the roles and responsibilities of the IT security team. Employing a template ensures a comprehensive approach to policy creation, allowing for customization to reflect the specific security needs of the organization while promoting a clear, mutual understanding of the preventive measures and actions required.
Key Elements of a Cybersecurity Policy
A robust Cybersecurity Policy should thoroughly address:
- Purpose and Scope - Defines the goals of the policy and the extent to which it applies, including which parts of the organization are affected and the types of information it protects.
- Information Security Standards - Describes the standards and methodologies the organization adopts to protect its systems and data.
- User Access Control - Outlines the methods for granting, modifying, and revoking access to systems and data, emphasizing the principle of least privilege.
- Data Protection - Specifies the techniques for managing the security of data at rest, in transit, and in use.
- Incident Response - Establishes procedures for detecting, reporting, and responding to security incidents to minimize damage and recover operations.
- Employee Training and Awareness - Details the training programs to enhance security awareness among employees and ensure they understand their roles in maintaining cybersecurity.
- Regular Audits and Compliance - Calls for periodic reviews and audits of cybersecurity practices to ensure compliance with the policy and regulatory requirements.
Supporting Documents for Structuring a Cybersecurity Policy
To enhance the effectiveness and comprehensiveness of a Cybersecurity Policy, integrating related documents is advisable:
- Incident Response Plan - Provides a detailed action plan for handling security breaches or attacks to minimize impact and guide recovery efforts.
- Data Classification Policy - Helps in identifying the levels of sensitivity of data held by the organization and the corresponding security controls required.
- Acceptable Use Policy - Outlines the permissible uses of organizational technology and the consequences of policy violations.
Why Employ a Detailed Template for a Cybersecurity Policy?
Utilizing a detailed template for drafting your Cybersecurity Policy offers significant benefits:
- Risk Reduction - Minimizes the risk of cyber threats by establishing strong security practices and response strategies.
- Adaptability - Allows for tailoring the policy to the specific technological and operational context of the organization.
- Operational Continuity - Enhances the organization’s ability to prevent disruptions caused by cyber incidents and quickly restore normal operations.
- Regulatory Compliance - Ensures that the organization meets legal and regulatory requirements related to cybersecurity, protecting it from potential fines and legal actions.
Adopting a comprehensive Cybersecurity Policy is essential for protecting an organization’s information assets in an increasingly complex cyber threat landscape. It provides a clear, enforceable framework that outlines the responsibilities and expected behaviours of all members of the organization, ensuring a unified approach to maintaining digital security and integrity.
Updated in April 2024
Part of your Business Operating System
Reviewed on

Fortifying Digital Integrity with a Cybersecurity Policy
In today's digital age, where technology permeates every aspect of business operations, protecting information assets against cyber threats is paramount. A Cybersecurity Policy forms the backbone of an organization's security framework, establishing comprehensive guidelines that govern the use, management, and protection of electronic information.
This policy is a critical tool, outlining the standards for cybersecurity measures across the organization, including data protection protocols, access control mechanisms, and response strategies for security incidents. It not only ensures the safeguarding of confidential and sensitive information but also fosters a culture of security awareness and compliance among all employees. This document transcends traditional IT management; it is about embedding security into the very fabric of organizational operations to mitigate risks and maintain trust with stakeholders.
What is a Cybersecurity Policy Template?
A Cybersecurity Policy template serves as a structured guideline that details the essential components of establishing effective cyber defences. This includes the identification of critical information assets, risk management procedures, security practices for employees, and the roles and responsibilities of the IT security team. Employing a template ensures a comprehensive approach to policy creation, allowing for customization to reflect the specific security needs of the organization while promoting a clear, mutual understanding of the preventive measures and actions required.
Key Elements of a Cybersecurity Policy
A robust Cybersecurity Policy should thoroughly address:
- Purpose and Scope - Defines the goals of the policy and the extent to which it applies, including which parts of the organization are affected and the types of information it protects.
- Information Security Standards - Describes the standards and methodologies the organization adopts to protect its systems and data.
- User Access Control - Outlines the methods for granting, modifying, and revoking access to systems and data, emphasizing the principle of least privilege.
- Data Protection - Specifies the techniques for managing the security of data at rest, in transit, and in use.
- Incident Response - Establishes procedures for detecting, reporting, and responding to security incidents to minimize damage and recover operations.
- Employee Training and Awareness - Details the training programs to enhance security awareness among employees and ensure they understand their roles in maintaining cybersecurity.
- Regular Audits and Compliance - Calls for periodic reviews and audits of cybersecurity practices to ensure compliance with the policy and regulatory requirements.
Supporting Documents for Structuring a Cybersecurity Policy
To enhance the effectiveness and comprehensiveness of a Cybersecurity Policy, integrating related documents is advisable:
- Incident Response Plan - Provides a detailed action plan for handling security breaches or attacks to minimize impact and guide recovery efforts.
- Data Classification Policy - Helps in identifying the levels of sensitivity of data held by the organization and the corresponding security controls required.
- Acceptable Use Policy - Outlines the permissible uses of organizational technology and the consequences of policy violations.
Why Employ a Detailed Template for a Cybersecurity Policy?
Utilizing a detailed template for drafting your Cybersecurity Policy offers significant benefits:
- Risk Reduction - Minimizes the risk of cyber threats by establishing strong security practices and response strategies.
- Adaptability - Allows for tailoring the policy to the specific technological and operational context of the organization.
- Operational Continuity - Enhances the organization’s ability to prevent disruptions caused by cyber incidents and quickly restore normal operations.
- Regulatory Compliance - Ensures that the organization meets legal and regulatory requirements related to cybersecurity, protecting it from potential fines and legal actions.
Adopting a comprehensive Cybersecurity Policy is essential for protecting an organization’s information assets in an increasingly complex cyber threat landscape. It provides a clear, enforceable framework that outlines the responsibilities and expected behaviours of all members of the organization, ensuring a unified approach to maintaining digital security and integrity.
Updated in April 2024
Create Standard Documents That Define How Your Business Runs.
Agreements, policies, and plans — all structured inside one Business Operating System.
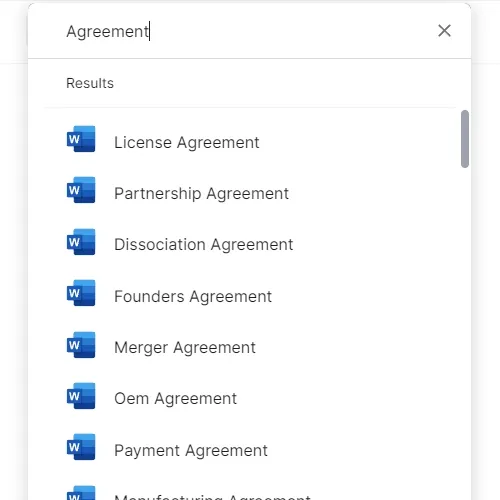
Download or open template
Access over 3,000+ business and legal templates for any business task, project or initiative.
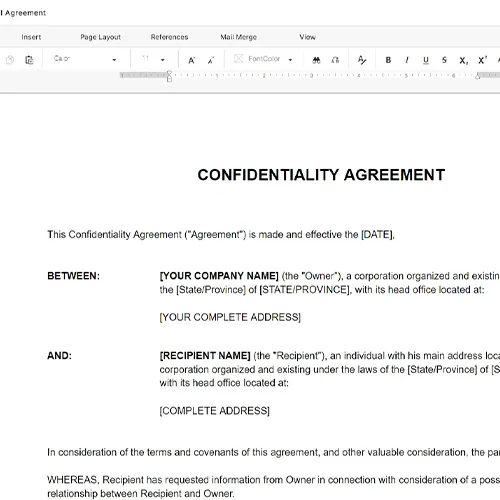
Edit and fill in the blanks
Customize your ready-made business document template and save it in the cloud.
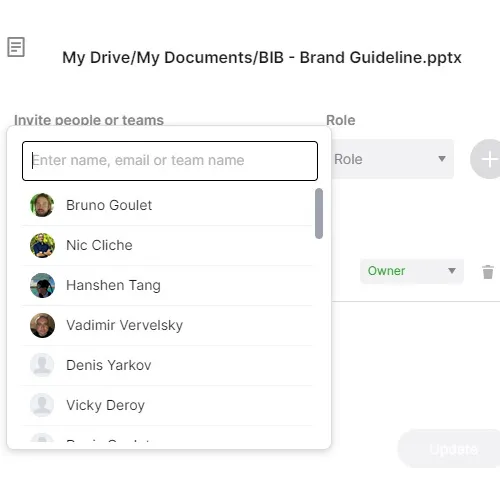
Save, Share, Export, or Sign
Share your files and folders with your team. Create a space of seamless collaboration.
Run Your Business With a System — Not Scattered Tools
Stop downloading documents. Start operating with clarity. Business in a Box gives you the Business Operating System used by over 250,000 companies worldwide to structure, run, and grow their business.


