1
Identify the parties and confirm IP ownership
Enter the full registered legal names and jurisdictions of both the transferor and transferee. Before signing, confirm the transferor holds clear title to every element of the licensed technology — check patent assignment records at the USPTO and corporate IP assignment agreements with employees and contractors.
💡 Run a quick USPTO assignment database search on the patent numbers in Schedule A to confirm recorded ownership matches the transferor entity named in the agreement.
2
Define the licensed technology in a detailed schedule
Draft Schedule A listing each patent by number, Schedule B identifying software by version and repository hash, and Schedule C describing trade secrets and know-how by category. Attach all schedules before execution.
💡 For software transfers, include a SHA-256 hash of the specific codebase version in Schedule B — this creates an immutable record of exactly what was transferred and when.
3
Choose and document the license type and scope
Decide whether the grant is exclusive or non-exclusive, worldwide or territory-limited, and whether sublicensing is permitted. Draft a field-of-use schedule if the transferor intends to retain rights in adjacent markets.
💡 If you are granting an exclusive license, confirm you have no existing non-exclusive licenses to the same technology that would conflict — check all prior agreements before drafting.
4
Set the royalty structure and define Net Sales
Enter the upfront fee, royalty rate, and the definition of Net Sales that the royalty applies to. Explicitly exclude returns, taxes, and distributor allowances from the royalty base. Add milestone payment triggers in Schedule E.
💡 Benchmark your royalty rate against published industry standards — pharmaceutical licenses typically run 3–10% of net sales; software licenses often use a flat per-seat fee instead of a percentage.
5
Address sublicensing, improvements, and grant-back
Decide whether the transferee may sublicense and under what approval process. Allocate ownership of improvements — sole, joint, or grant-back — and confirm both parties understand the implications before finalizing the language.
💡 If the transferee will sublicense to distributors, require a standard sublicense agreement form as an exhibit so every sublicense is automatically consistent with the main agreement.
6
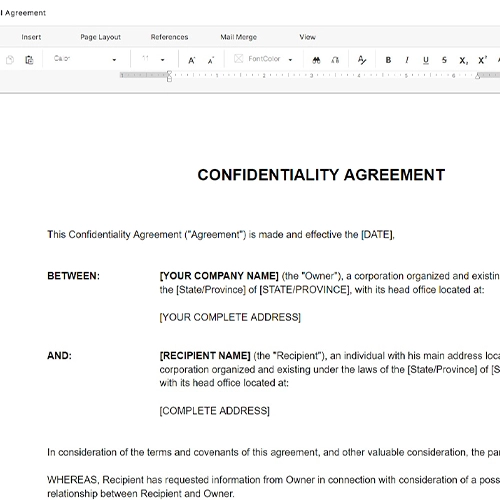
Draft the confidentiality and survival provisions
Set the confidentiality standard, the categories of excluded information, and the post-termination survival period. For core trade secrets, consider a perpetual confidentiality obligation rather than a fixed term.
💡 Specify in writing which employees and contractors of each party are permitted to access confidential technical information — limiting access by role reduces leak risk and strengthens enforceability.
7
Complete the termination and export control clauses
Define termination triggers (material breach, insolvency, change of control), the cure period, and what happens to sublicenses and accrued royalties post-termination. If any element of the technology is subject to EAR, ITAR, or EU dual-use controls, add the export compliance clause.
💡 Consult an export control attorney before finalizing any transfer involving encryption software, defense-related hardware, or technology licensed to a foreign national — even a royalty-free academic license can require government approval.
8
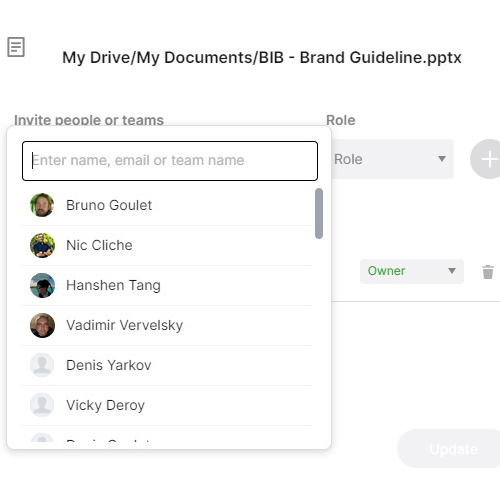
Execute before any technology access is provided
Both parties must sign before any confidential technical information, source code, or patent documentation is shared. Post-disclosure signatures create enforceability gaps, particularly on confidentiality and IP ownership.
💡 Use a timestamp-verified eSignature platform and store the fully executed agreement alongside all schedules in a single version-controlled file to prevent schedule substitution disputes.