1
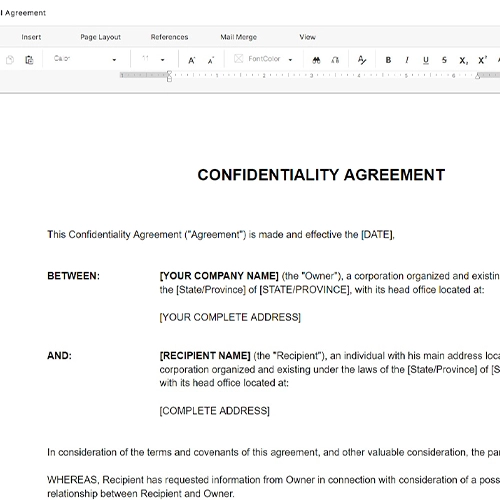
Identify both parties with full legal names
Enter the company's registered legal name — not a brand or product name — and the beta tester's full legal name as it appears on government ID. For business entities acting as testers, include the entity type and registration jurisdiction.
💡 For remote or anonymous testers, collect identity verification before issuing credentials — an NDA signed by 'JohnDoe99' is unenforceable.
2
Define the scope of confidential information precisely
List every category of information the tester will access: pre-release software builds, design mockups, feature specs, pricing data, roadmap slides, and any oral briefings. The more specific the list, the easier it is to prove a breach.
💡 Add a catch-all phrase after the list — 'and any other non-public information disclosed in connection with the beta program' — to cover items not explicitly enumerated.
3
Set the testing period and confidentiality tail
Enter the start and end date of the beta program. Then set the post-termination confidentiality period — 2 years is standard for software betas; 3 years for hardware or enterprise products with longer competitive cycles.
💡 Tie the confidentiality tail to a specific date rather than a relative period — 'until December 31, 2028' is clearer than '2 years from termination' and easier to enforce.
4
Include the IP assignment and feedback clause
Confirm the clause assigns all feedback, bug reports, and feature suggestions to the company effective immediately upon creation. Have the tester initial this clause separately if your jurisdiction requires explicit acknowledgment for IP assignments.
💡 If you are running a paid beta, add a sentence confirming that any compensation paid is in exchange for both testing services and the IP assignment — this prevents a later claim that the assignment lacked consideration.
5
Tailor the permitted use restriction
Specify that the tester may only use the beta build on approved devices, may not reverse-engineer or decompile it, and may not benchmark it against competing products without written consent.
💡 For mobile betas, add a clause prohibiting screen recording and screenshot sharing, which are the most common leak vectors.
6
Add the return or destruction obligation
Require that the tester delete the beta software, revoke credentials, and return or destroy any physical materials within 5 business days of the program's end. Include a written certification requirement.
💡 For enterprise or hardware betas, specify a witnessed destruction procedure or require proof of data-wiping software output.
7
Confirm governing law matches the enforceability landscape
Choose the governing law based on where your company is incorporated and where the tester is located. If testers are in California, check that your confidentiality obligations comply with California trade secret law.
💡 For international beta programs, consider adding a separate exhibit addressing EU GDPR obligations if testers are based in Europe.
8
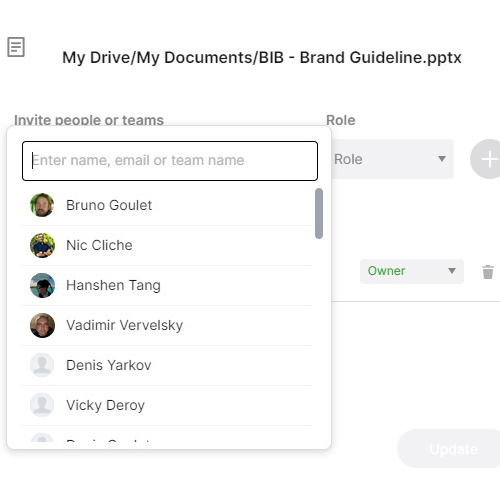
Execute before issuing access credentials
Both parties must sign the agreement before the tester receives any beta build, login, or documentation. Use e-signature with a timestamp to create an audit trail. Never distribute credentials first and follow up with paperwork later.
💡 Send the NDA as a signing link via Business in a Box eSign so the timestamp and IP address of execution are captured automatically.