1
Identify both parties with their full legal names
Enter the registered legal name of the disclosing party (your business) and the receiving party (employee, contractor, or partner). Confirm the entity type — LLC, corporation, sole proprietor, or individual.
💡 Cross-reference your state or provincial corporate registry to confirm the exact registered name before execution — a name mismatch can void enforcement.
2
Define confidential information with specific categories
List the specific categories of information you are protecting — client lists, pricing models, source code, financial projections, product formulas. Avoid both 'all information' (overbroad) and named documents only (too narrow).
💡 Include both written and oral disclosures in the definition — deals frequently involve verbal conversations that fall outside agreements limited to written materials.
3
Set the non-compete scope: geography, industry, and duration
Define the geographic area (city, state, country, or radius in miles/km), the specific business activities that are restricted, and the duration following the end of the relationship. Match the scope to the receiving party's actual role and access.
💡 For a sales representative with a regional territory, a 50-mile radius and 12-month restriction is more defensible than a nationwide, 24-month ban.
4
Draft the non-solicitation terms for customers and employees
Specify which customers are covered — typically those the receiving party had direct contact with — and limit the employee non-solicit to active solicitation rather than a ban on hiring anyone who applies independently.
💡 A non-solicitation limited to customers the receiving party actually serviced is consistently upheld; a ban on all contact with any company customer is frequently voided.
5
State the permitted purpose for confidential information
Write a single, specific sentence describing the only authorized use for the shared information — for example, 'evaluating a potential employment relationship' or 'performing software development services under Statement of Work #[X].'
💡 A vague permitted purpose like 'business purposes' defeats the clause — the more specific the use case, the easier a breach is to prove.
6
Include the return-or-destroy obligation with a deadline
Require the receiving party to return all confidential materials — physical and digital — or provide written certification of destruction within a specific number of days of termination or request.
💡 Specify that electronic copies, backups, and cloud storage are included in the return-or-destroy obligation — most breaches today involve digital files, not paper documents.
7
Select the governing law based on the receiving party's location
Choose the jurisdiction where the receiving party primarily works, not where your business is incorporated. Courts in the receiving party's jurisdiction will typically apply local employment law regardless of the contract's choice-of-law clause.
💡 If the receiving party works in California, Minnesota, or North Dakota, consult a lawyer before finalizing — these states ban or severely restrict non-competes.
8
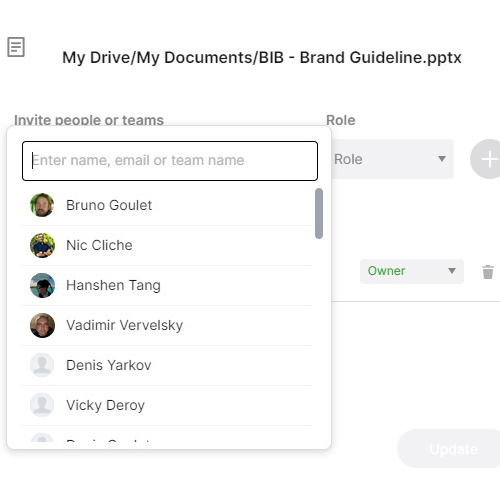
Execute before the relationship begins and retain a signed copy
Both parties must sign before the employee starts work, the contractor accesses systems, or the confidential information is shared. Post-commencement signatures require fresh consideration in common-law jurisdictions to be enforceable.
💡 Use a timestamped eSignature platform so the execution date is documented and cannot later be disputed.