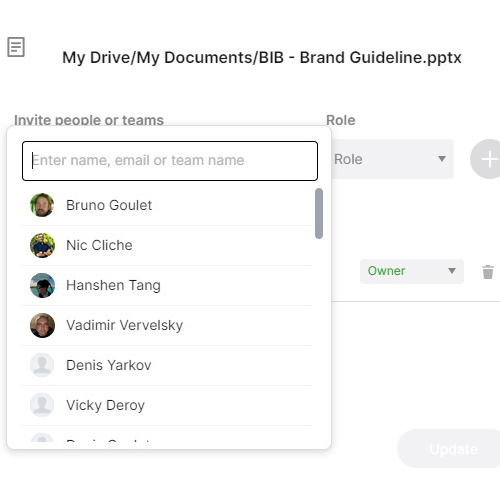
- Key Holder
- An employee authorized by an employer to hold physical keys and/or alarm codes granting independent access to business premises outside of normal staffing hours.
- Opening Procedures
- A documented checklist of tasks an employee must complete when unlocking and preparing the premises for business — including alarm disarming, safety checks, and cash drawer setup.
- Closing Procedures
- A documented checklist of tasks performed at the end of the business day — including cash reconciliation, securing the premises, setting the alarm, and locking all access points.
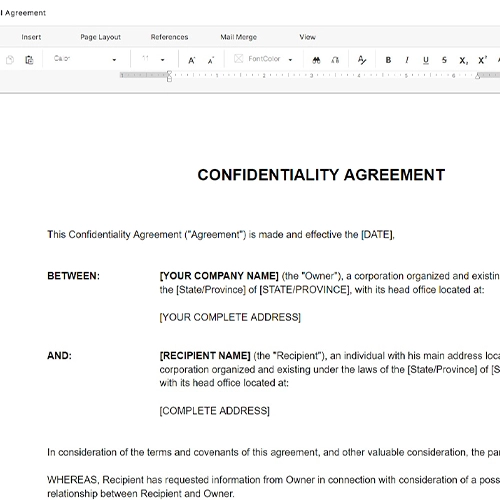
- Alarm Code
- A numeric or alphanumeric credential used to arm or disarm a security system; treated as confidential and assigned to specific authorized individuals only.
- Cash Reconciliation
- The process of counting and verifying cash drawer or safe contents against recorded transactions at the start or end of a shift to identify discrepancies.
- Safe Combination
- The access credential for a physical safe on the premises; typically restricted to key holders, managers, and designated authorized personnel.
- Escalation Protocol
- A predefined sequence of contacts and actions an employee must follow when a security incident, alarm trigger, or discrepancy occurs outside normal management hours.
- Duty of Care
- The legal obligation an employee in a position of trust has to take reasonable steps to protect the employer's property, assets, and other personnel.
- Access Credential
- Any form of authentication — physical key, key fob, PIN, or digital code — that grants entry to a secured space or system.
- Breach of Trust
- Conduct by an employee in a fiduciary or trusted position that violates the confidence placed in them — such as sharing alarm codes or failing to secure premises — which may constitute grounds for termination.