1
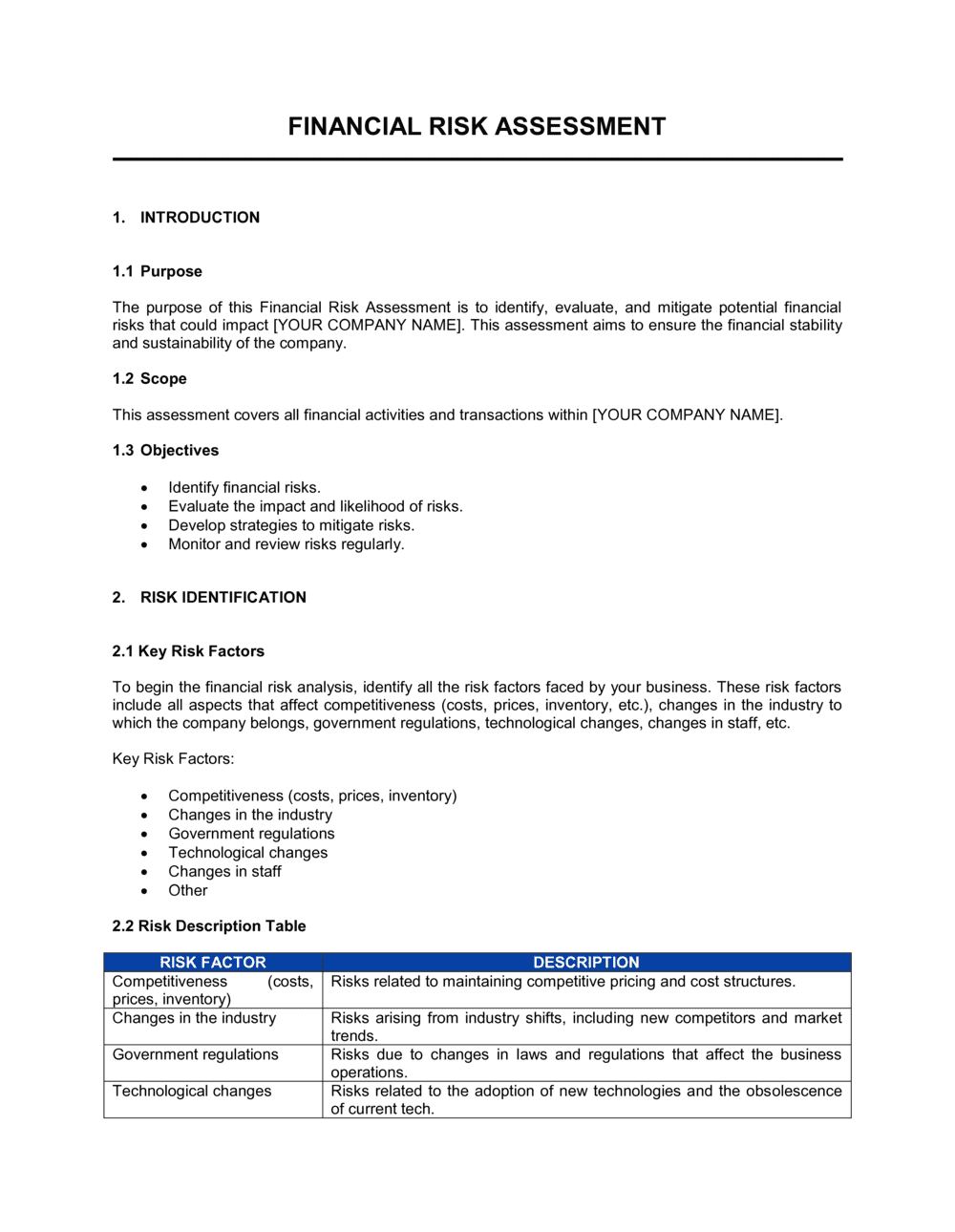
Define the scope, purpose, and assessment period
Enter the legal entity name, the business units covered, the time period under review, and the stated purpose — regulatory filing, board review, lender submission, or investor due diligence. Be explicit about what is excluded and why.
💡 A clearly stated scope prevents scope creep during the review process and sets the auditor's or investor's expectations before they read a single risk entry.
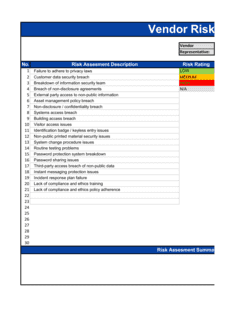
2
Identify all material financial risks by category
Work through each risk category — credit, liquidity, market, operational, and compliance — and list every specific exposure at the transaction, counterparty, or process level. Pull data from your accounts-receivable aging, cash flow forecasts, debt covenants, and management accounts.
💡 Involve at least one person from finance, one from operations, and one from the business unit being assessed — risks identified by a single function routinely miss the exposures other teams consider obvious.
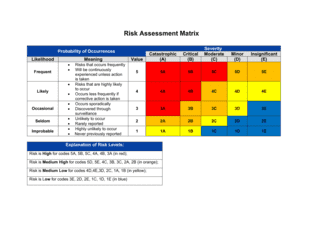
3
Score probability and impact for each risk
Assign a 1–5 probability score based on historical frequency or forward-looking likelihood, and a 1–5 impact score based on estimated financial loss in dollar terms. Multiply to produce the inherent risk rating.
💡 Anchor impact scores to specific dollar ranges agreed in advance — for example, score 3 = $50K–$500K loss, score 4 = $500K–$2M — so ratings are comparable across risk types and reviewers.
4
Document existing controls and rate their effectiveness
For each risk, describe what is actually in place today — policies, system controls, insurance, hedges, or manual processes — and rate effectiveness as strong, moderate, or weak based on the last time the control was tested or triggered.
💡 If a control has not been tested in the past 12 months, rate it as weak by default and flag it for testing in the mitigation action plan.
5
Calculate residual risk and compare to tolerance
Recalculate probability and impact scores after applying control effectiveness, produce the residual rating, and compare it against your organization's stated risk tolerance threshold. Flag every risk that exceeds the threshold.
💡 If your organization has not formally defined a risk tolerance, set a provisional threshold — for example, any residual score above 9/25 requires a mitigation action — and have the board ratify it when approving the assessment.
6
Build the mitigation action plan for above-threshold risks
For every risk exceeding the tolerance threshold, write a specific action, assign it to a named individual (not a team), set a completion deadline, and define a measurable success metric.
💡 Deadlines longer than 90 days should be broken into interim milestones — a single 12-month deadline creates no accountability pressure and is rarely met.
7
Define KRIs and the monitoring schedule
Select one to three measurable indicators for each high and medium residual risk, set alert and breach thresholds, and establish the reporting frequency and escalation path.
💡 KRIs should be available from existing systems — ERP, banking portal, or accounting software — without manual data collection. If you cannot automate the data pull, the KRI will not be monitored consistently.
8
Obtain individual risk-owner sign-offs and board approval
Circulate the assessment to each named risk owner for individual acknowledgment, then present the completed document to the board or audit committee for formal approval before filing or distributing externally.
💡 Schedule the board approval meeting before distributing the assessment to lenders or investors — an unapproved draft shared externally creates governance risk and may breach confidentiality obligations.