- Employee Monitoring
- The use of technology or processes by an employer to observe, record, or measure an employee's work activities, communications, or computer usage during work hours.
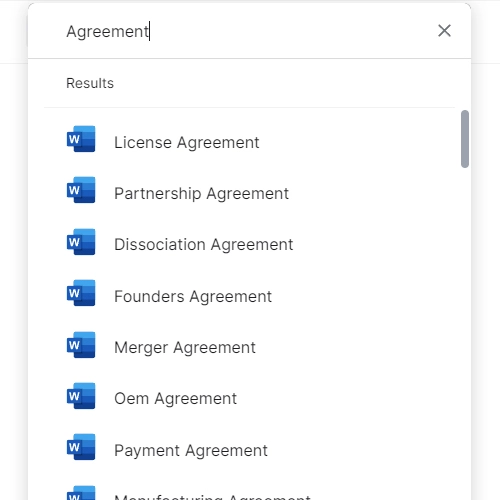
- Acceptable Use Policy (AUP)
- A written policy specifying what employees may and may not do with company-owned devices, networks, and software.
- Keystroke Logging
- Software that records every key pressed on a computer keyboard, used to track employee activity but considered highly intrusive in most employment contexts.
- Screen Capture Monitoring
- Periodic or continuous screenshots of an employee's computer screen taken by monitoring software to verify work activity.
- Time Tracking
- Recording the hours an employee works, including start and end times and breaks, using software, apps, or manual logs.
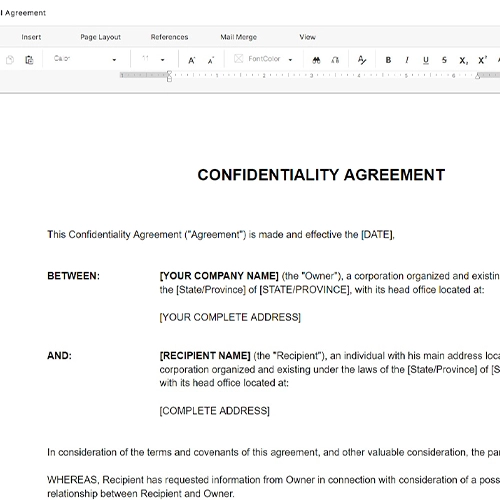
- Informed Consent
- A process by which an employee is clearly notified of what monitoring will occur and acknowledges this in writing before monitoring begins.
- Data Minimization
- The principle of collecting only the employee data necessary for the stated monitoring purpose and retaining it no longer than needed.
- Productivity Metrics
- Quantifiable measures of work output — such as tasks completed, response times, or hours logged — used to evaluate remote employee performance.
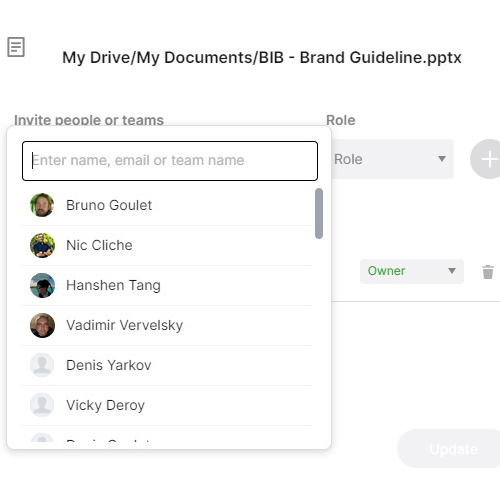
- Bring Your Own Device (BYOD)
- A policy allowing employees to use personal devices for work, which creates complex boundaries for what an employer may legally monitor.
- Right to Privacy
- An employee's legally and ethically recognized interest in keeping personal communications and activities free from employer surveillance, even during work hours.
- Surveillance Creep
- The gradual expansion of monitoring scope beyond its original purpose, often eroding employee trust and increasing legal exposure over time.